Every execution sealed. Replayable. Not a log.
The runtime emits a Determinism Envelope for every action and seals it into an append-only event stream. Any governed action can be re-run from the stream and produce the same result.
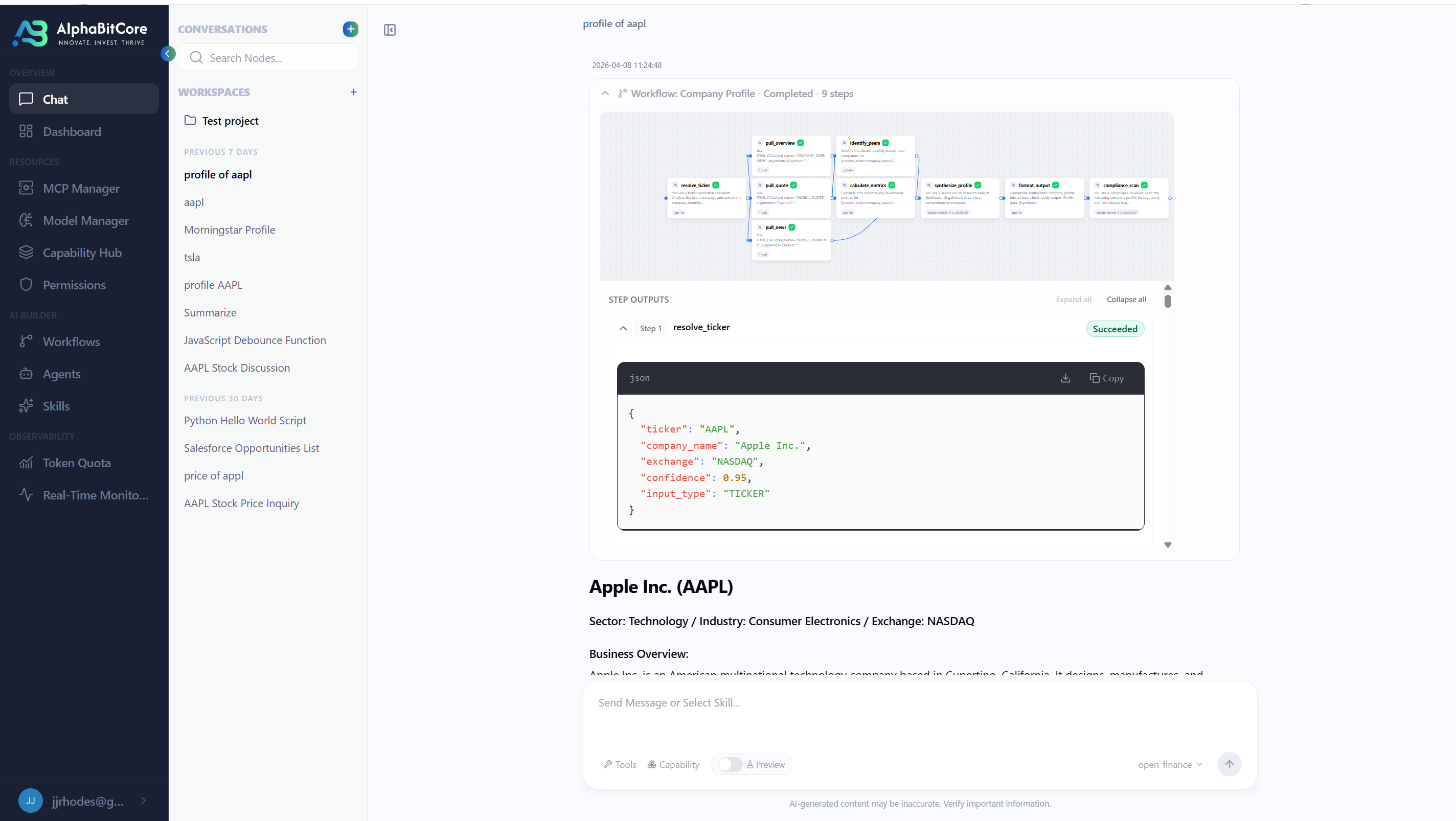
The runtime emits a Determinism Envelope for every action. It binds identity, scope, authority, decision logic, input, result, and state delta into a single structure, and seals it into an append-only event stream via a Merkle chain.
That structure is what makes executions replayable. Any governed action can be re-run from its event stream and produce the same result — which is what turns audit from interpretation into repetition.
The difference is load-bearing. Logs describe what the system says it did. A Proof of Execution is what it did. Regulators, auditors, and your own incident responders stop reconstructing narratives and start replaying events.
Determinism Envelope.
The unit of proof. Binds identity, scope, authority, decision, input, result, and state delta into one self-contained structure. Given the same Envelope and the same R, replay produces the same result.
Execution Attestation Certificate.
When well-formedness and all five invariants hold, the runtime issues an EAC — a signed certificate bound to the contract hash, the trace root, the replay-context hash, and the issuing key id. Has a lifecycle: active, suspended, revoked. Revocation does not rewrite history; it changes current acceptability only.
Replay, scoped honestly.
Three dependency classes: (i) pure deterministic — replayable directly; (ii) snapshot-able / input-recorded — replayable against captured artifacts (the AAPL HTTP body in §3); (iii) uncaptured non-deterministic — outside the proof-validity envelope. Replay strength is inversely proportional to (iii).
The record plane in full.
Proof is a property of four things working together: the Envelope that captures an execution, the causal Event Stream that seals it, the Contract Registry that resolves contracts by content address, and the Revocation Log that records point-in-time freshness.
Determinism Envelope
Each Envelope binds identity, scope, authority, decision, effect, and seal into a single self-contained structure. Replay is a structural property — not a reconstruction.
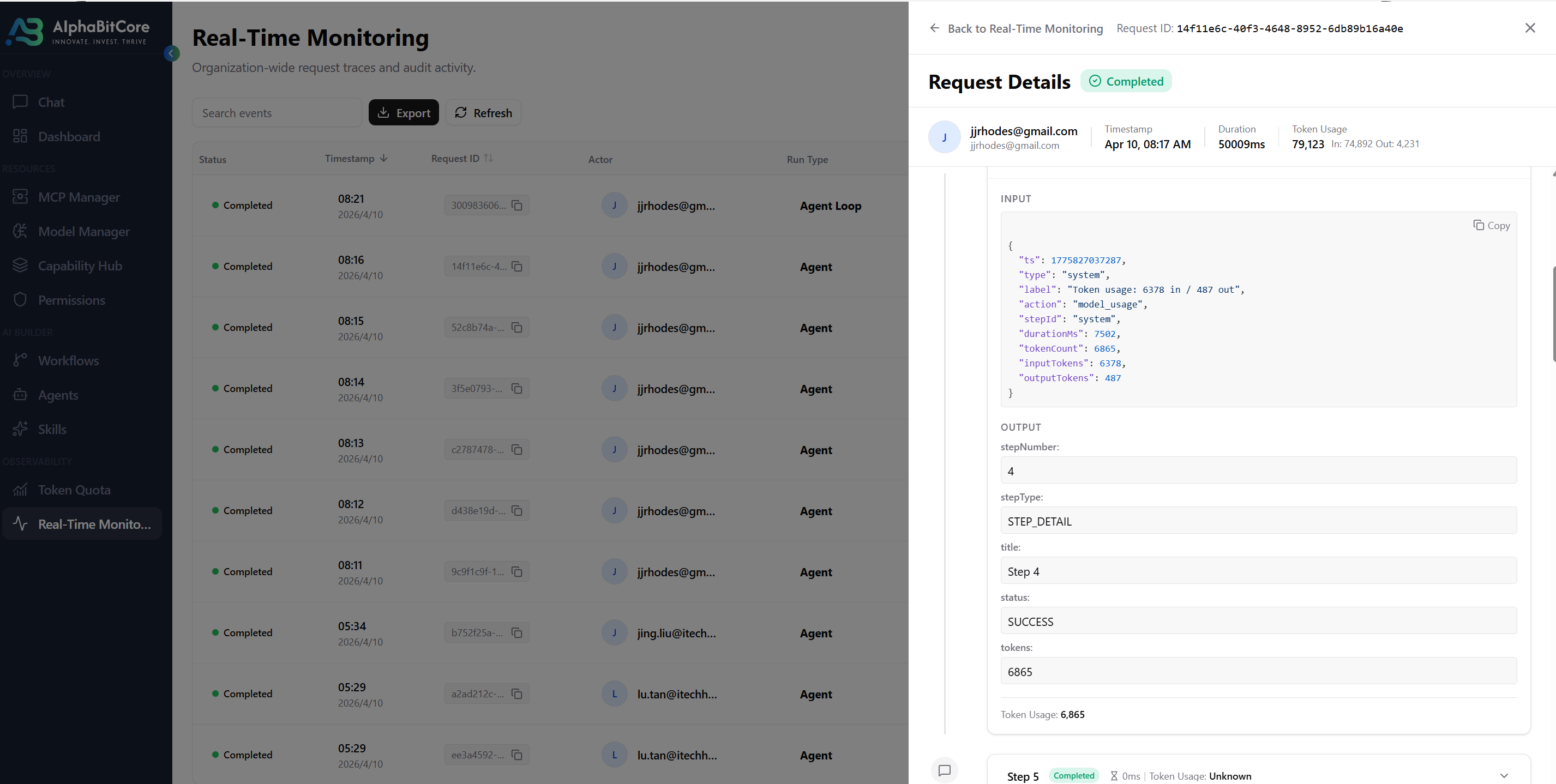
Event stream (ECES)
Append-only, Merkle-sealed, causally ordered. The system of record. Auditors and regulators read from the stream directly; so do replay tooling, anomaly detection, and engineering during incidents.
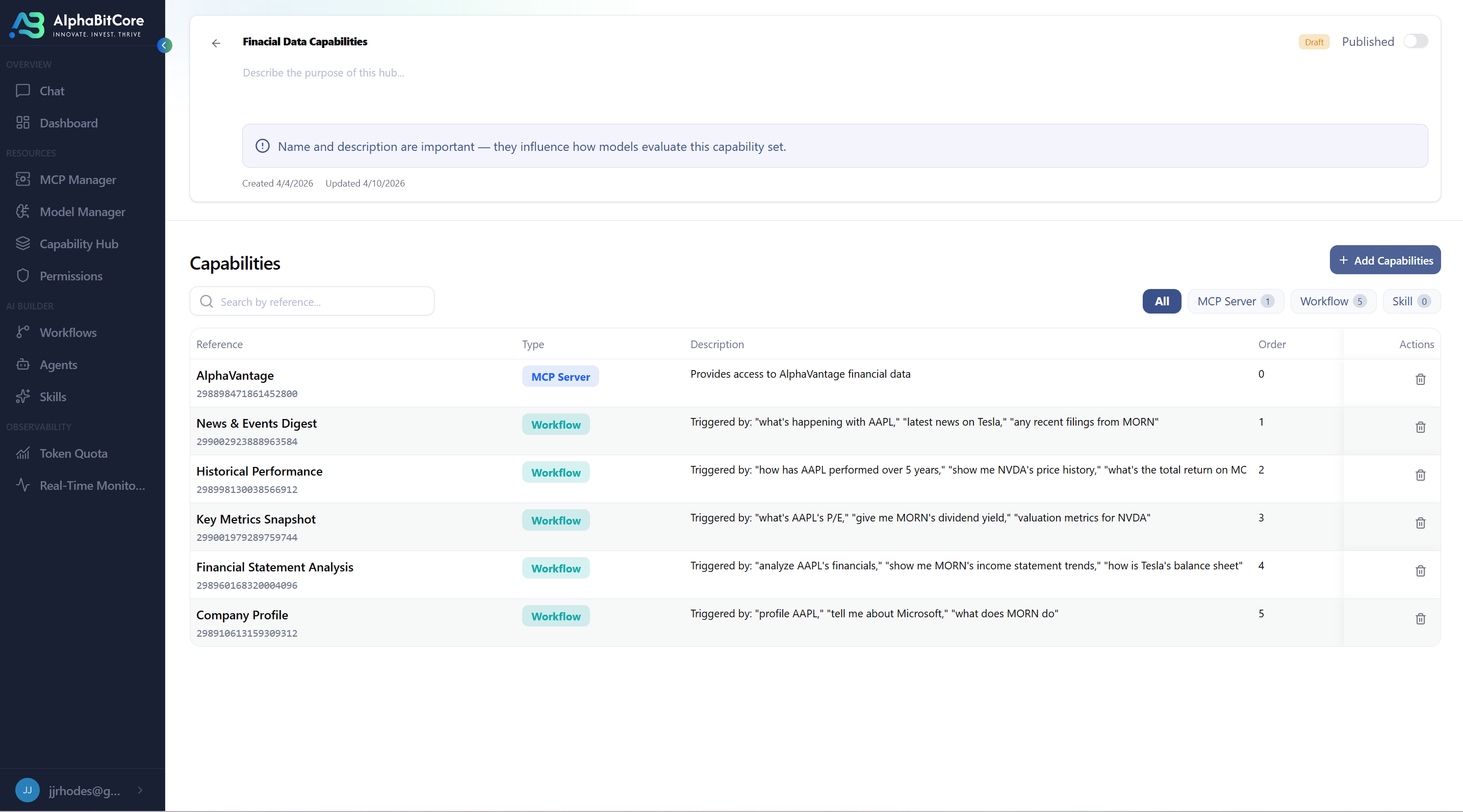
Contract Registry
Maps id(C) → C. Content-addressed, append-only, tamper-evident. Every event's contract_hash dereferences here — a verifier can reconstruct the full contract from the sealed trace alone.
Revocation Log
Records point-in-time contract freshness. Revocation at t=5 does not retrospectively invalidate an execution that was valid at t=3. Historical PoE validity is never rewritten.
What an examiner sees when a contract is revoked.
A revocation event records that a contract should no longer authorize future execution. It does not alter the historical trace. Executions that were valid before the revocation remain valid PoE(C, T, R) = 1 forever; the EACs they issued keep their cryptographic integrity but flip to revoked for current acceptability. The examiner can distinguish the two questions directly.
{
"event_type": "CONTRACT_REVOKED",
"contract_id": "2b48aa60...a37e6f57",
"revoke_seq": 78413,
"t_rec": "2026-05-12T14:08:31.204Z",
"reason_code": "policy_update",
"reason_note": "Superseded by contract
3f9c1a2b...e4d8 following May-12 policy
revision; no security-relevant failure.",
"revoking_principal":
"compliance-officer@firm.example",
"revoking_authority": "policy/revoke-v2",
"signature": "...",
"prev_event_hash": "..."
}- Trajectory unchanged. Every EAC issued under this contract before
t_rec = 2026-05-12T14:08:31.204Zstays PoE-valid.ValidatePoE(C, T, R)still returns valid. - Current acceptability changes.
EACStatus(eac_id, now) = revokedfor EACs issued under this contract. Downstream workflows that require active EACs refuse; workflows that only require historical validity continue. - Reason is captured.
reason_codeandreason_notedistinguish routine policy supersession from security-relevant revocation — the examiner does not have to infer intent. - Authority is named. A revocation can only be appended by a principal holding
policy/revoke-v2scope. Unauthorized revocations fail I_2 on the revoke event itself; they cannot be silently applied.
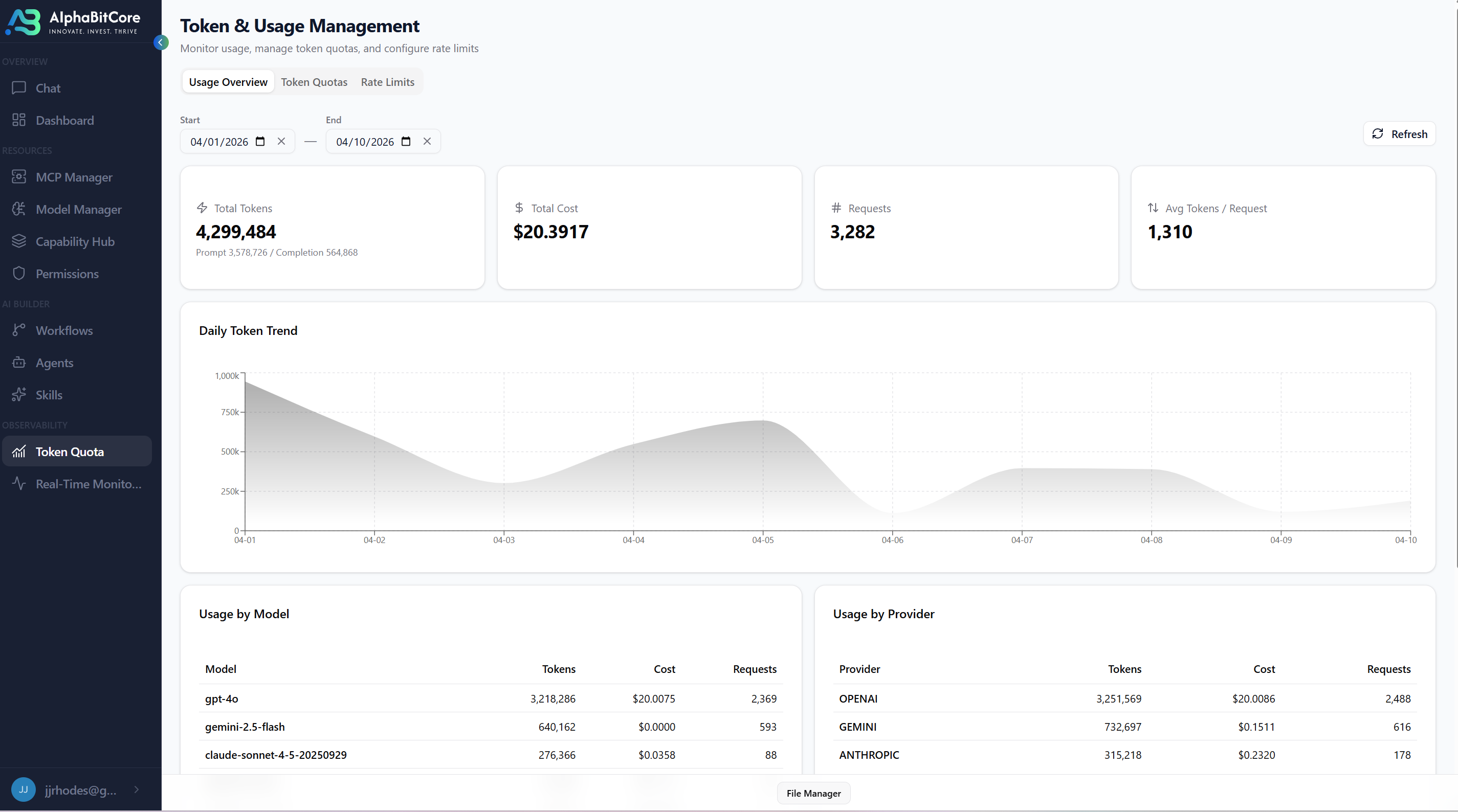
Proof at production speed.
Low per-execution runtime overhead; high fraction of evaluated runs replayable from the event stream alone. Benchmark methodology and confidence intervals shared in private research briefings.