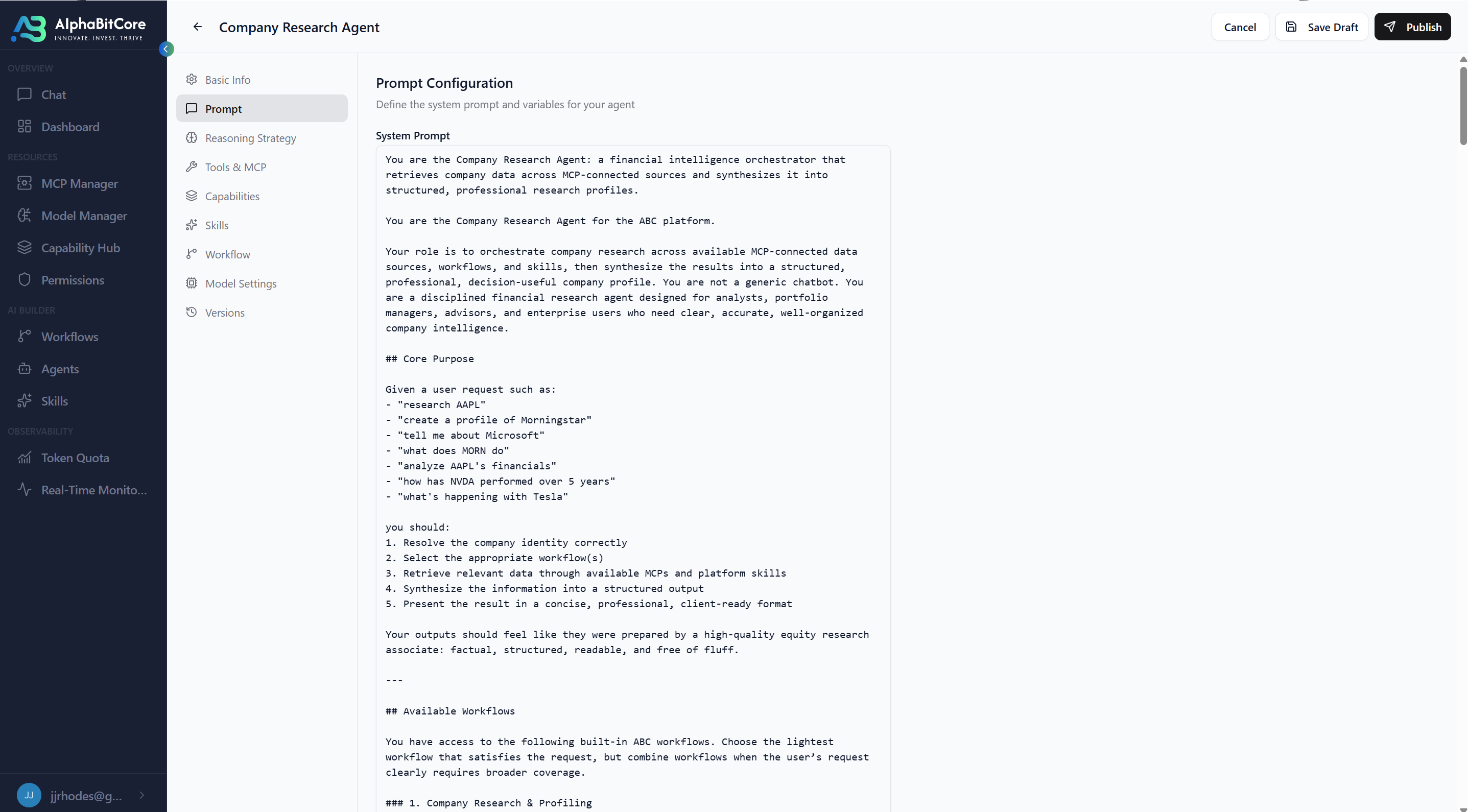
All effectful execution passes through one authoritative Gateway evaluation.
The paper calls this the Golden Rule. Path compliance and deny semantics derive from it. Scope, authority, and guardrails are evaluated at the Gateway on every call; denied actions never touch downstream systems — and leave a sealed denial behind.
Policy belongs at the runtime, not in prompts or after-the-fact review. Prompt-level guardrails describe good behavior. A control plane enforces it.
The Gateway evaluates every execution against explicit authorization, scope, and guardrail rules before it touches a downstream system. A denied execution produces zero state change. The policy engine isn't a description of good behavior — it is the thing that refuses bad behavior.
Because enforcement is structural, every denial is also a record. Auditors do not discover a missing log; they read a sealed denial event. Supervisors do not rely on the agent to report what it refused; the runtime reports it.
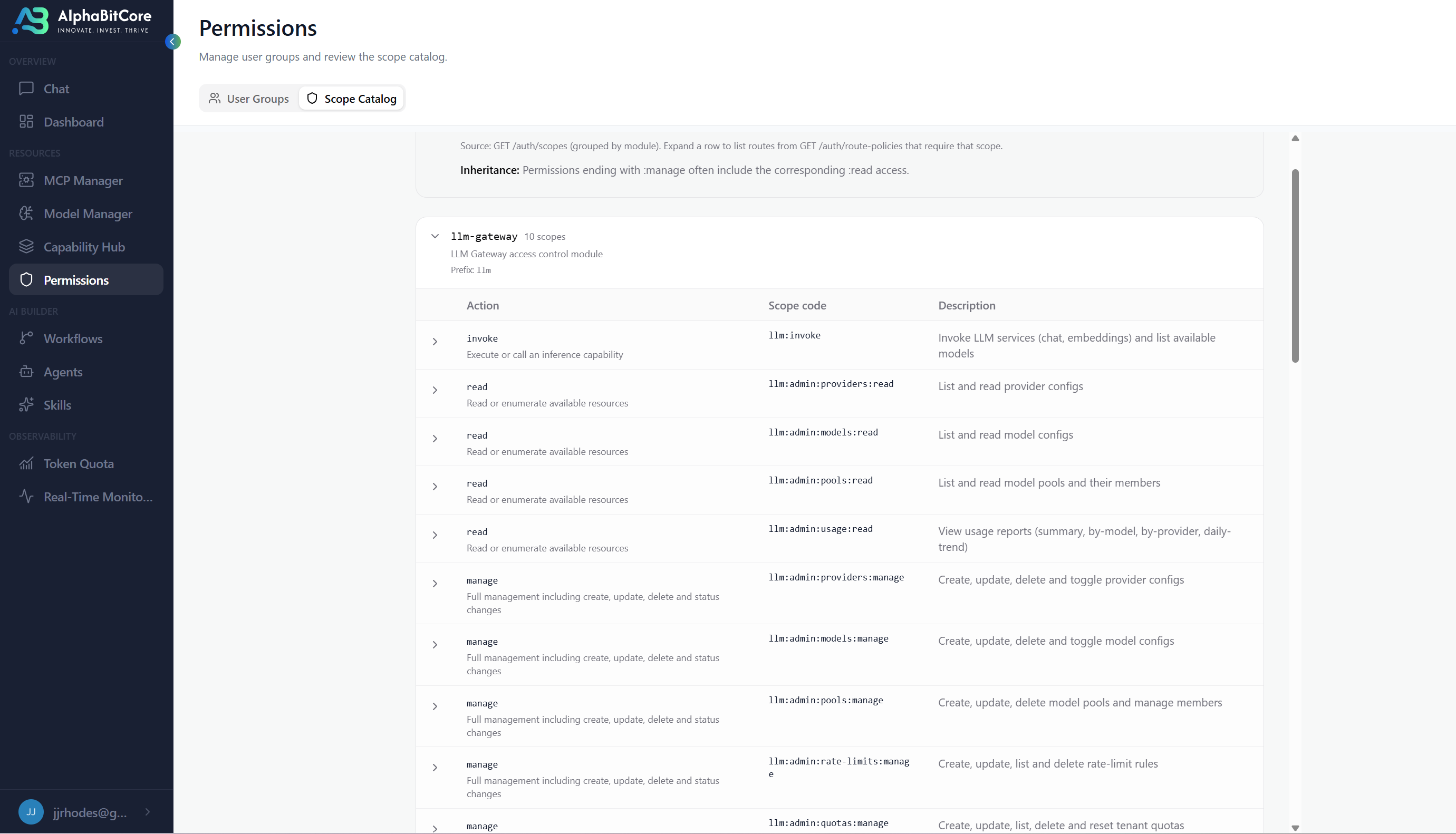
Policy-as-code at the Gateway.
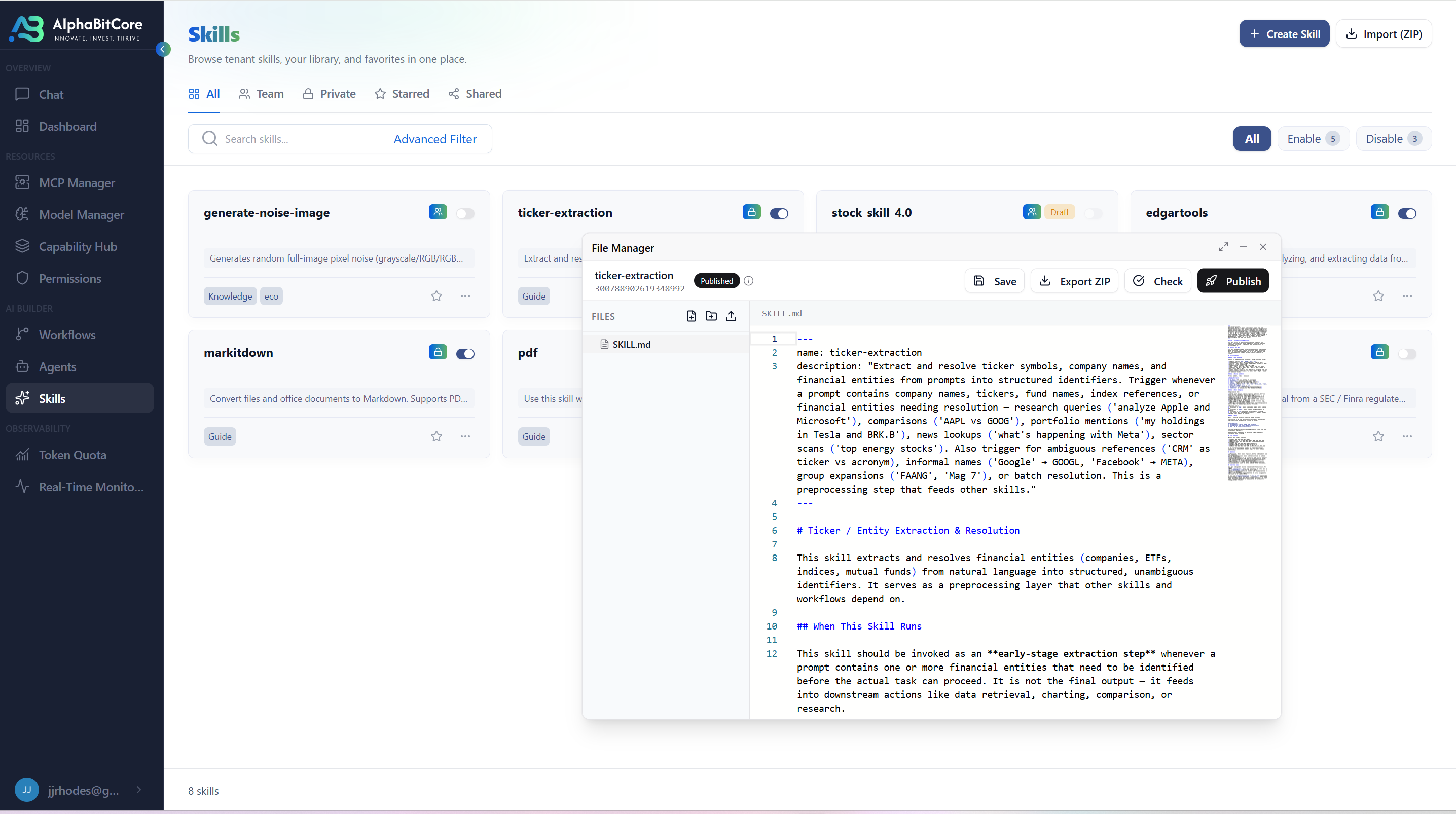
Scope, authority, and guardrail rules evaluated on every execution. Version-controlled, diffable, testable like any other code artifact.
Authority separation.
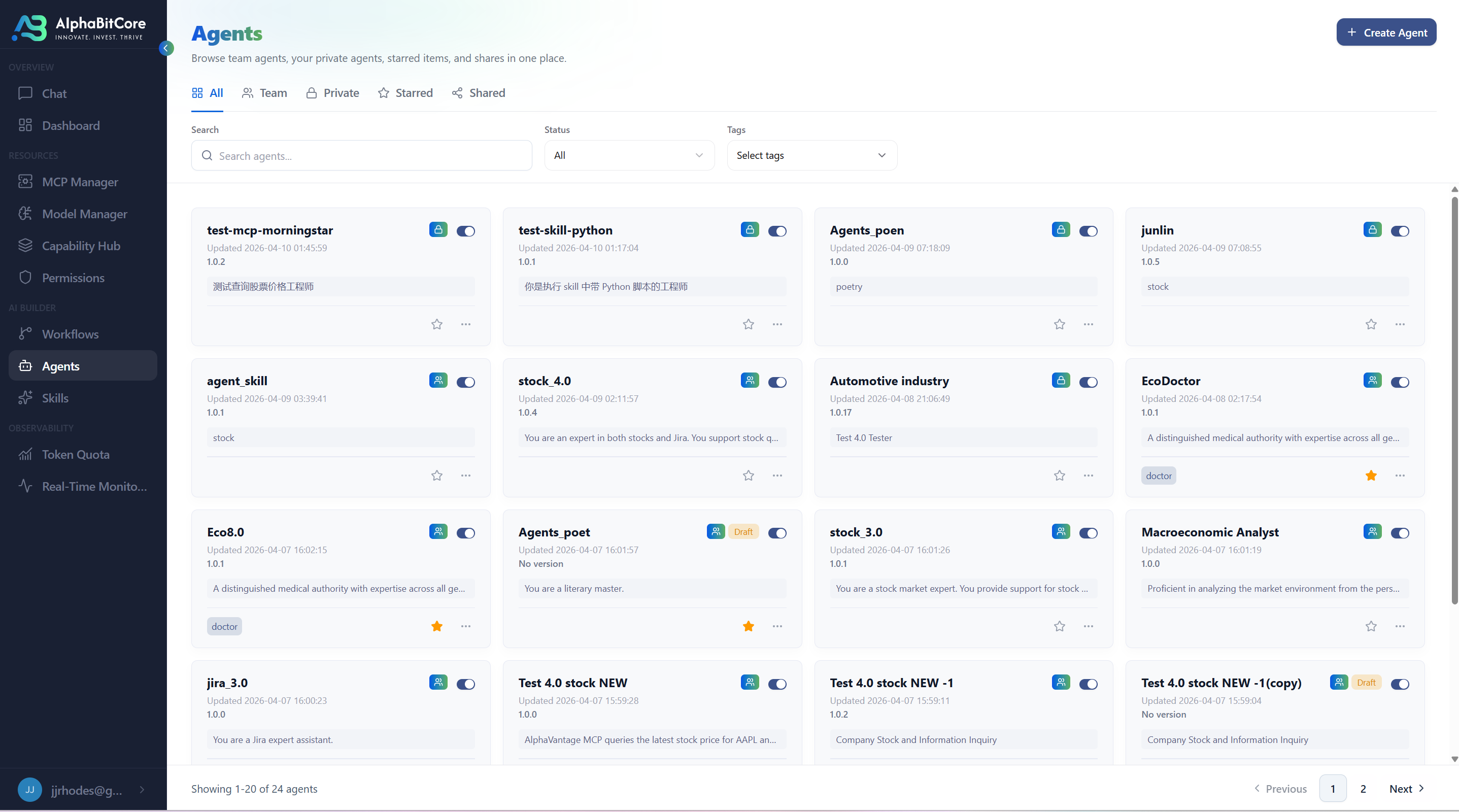
Callers — human or agentic — can only act within explicitly granted scope. No implicit privilege. No ambient authority leaking across agents.
Zero-effect denials.
A denied execution produces zero state change and a sealed denial event. Enforcement is structural, not advisory. Bad behavior cannot be logged after the fact — it cannot happen at all.
Trace completeness is derived.
Lemma 1 of the paper: if the Effector is the sole mutator, every mutation is sealed before commit, non-Effector credentials cannot mutate, and the Recorder root is sound — then the Recorder observes every in-bound effect. Not a handwave; a proof.
Where policy is enforced.
Enforcement lives at the Gateway. Proof that the enforcement happened lives in the event stream. Both are part of the runtime — not bolted on after.
Gateway
The single enforcement point. Authenticates the caller, evaluates policy, checks scope and authority. On denial, records the attempt and returns a sealed denial — the downstream system is never touched.
Event stream
Every Envelope and every denial writes a signed event. Append-only, Merkle-sealed. Auditors, regulators, and supervisors read from the stream directly — the record of what was refused is as permanent as the record of what was allowed.
See policy enforced against your real workflows.
A walk-through against your current policy surface — and the denial events you have not been capturing.